NVIDIA takes security concerns seriously and works to quickly evaluate and address them. Once a security concern is reported, NVIDIA commits the appropriate resources to analyze, validate and provide corrective actions to address the issue.
Contents
NVIDIA PSIRT – Vulnerability Management
Reporting Potential Security Vulnerability
Coordinated Vulnerability Disclosure
NVIDIA Acknowledgements
Subscribing to Security Bulletins and Updates
Media or PR Inquiries Regarding NVIDIA Security Vulnerability Information
NVIDIA PSIRT Vulnerability Management Process
Assessing Security Risk using Common Vulnerability Scoring System (CVSS)
Vulnerability Communication Policy
Security Bulletins
Security Notice
Vulnerability Remediation
NVIDIA PSIRT Participation
Customer Rights: Warranties, Support, and Maintenance
Disclaimer
NVIDIA PSIRT – Vulnerability Management
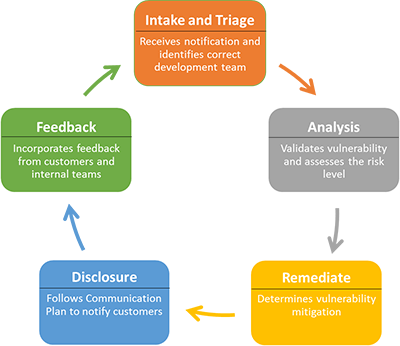
The NVIDIA Product Security Incident Response Team (PSIRT) goal is to minimize customers’ risk associated with security vulnerabilities by providing timely information, guidance and remediation of vulnerabilities in our products. NVIDIA PSIRT is a global team that manages the receipt, investigation, internal coordination, remediation and disclosure of security vulnerability information related to NVIDIA products.
One of the key responsibilities of NVIDIA’s PSIRT is to coordinate the response and disclosure for all externally identified NVIDIA product vulnerabilities.
Reporting Potential Security Vulnerability
Coordinated Vulnerability Disclosure
NVIDIA strives to follow Coordinated Vulnerability Disclosure (CVD). CVD is a process by which independent reporters who discover a vulnerability in our product contact NVIDIA directly and allow us the opportunity to investigate and remediate the vulnerability before the reporter discloses the information to the public.
NVIDIA PSIRT will coordinate with the reporter throughout the vulnerability investigation and will provide the reporter with updates on progress as appropriate. With the agreement of the reporter, NVIDIA PSIRT may recognize the reporter on our Acknowledgement page for finding a valid product vulnerability and privately reporting the issue. After an update or mitigation information is publicly released by NVIDIA, the reporter is welcome to discuss the vulnerability publicly.
Following NVIDIA’s CVD allows us to protect our customers and at the same time, coordinate public disclosures and appropriately acknowledge the reporter(s) for their finding.
If a reported vulnerability involves a vendor product, the NVIDIA PSIRT will notify the vendor directly, coordinate with the reporter, or engage a third-party coordination center.
NVIDIA Acknowledgements
While NVIDIA currently does not have a bug bounty program, we do offer acknowledgement when an externally reported security issue is addressed under our coordinated vulnerability disclosure policy.
- CVE number is granted for resolved issues in NVIDIA product code that require a customer to download a remediation. We also provide acknowledgment in the security bulletin for the issue.
- A mention on our acknowledgment website is provided for security issues addressed on our cloud services that do not require customers to download a fix for protection. PSIRT reserves the right to make the decision case-by-case.
Subscribing to Security Bulletins and Updates
The list of published Security Bulletins can be found on the NVIDIA Security Bulletins page.
Customers are strongly advised to subscribe to NVIDIA Security Bulletin notifications to stay informed of initial release or major revisions to NVIDIA Security Bulletins.
You can subscribe to notifications here.
For information about NVIDIA Security Bulletins, see the Security Bulletin section of this document.
Media or PR Inquiries Regarding NVIDIA Security Vulnerability Information
Please reach out to one of the Corporate Communication contacts listed here.
Assessing Security Risk using Common Vulnerability Scoring System (CVSS)
NVIDIA currently uses the Common Vulnerability Scoring System version 3.1 (CVSS v3.1) to evaluate the severity level of identified vulnerabilities. CVSS enables a common scoring method and a common language to communicate the characteristics and impacts of vulnerabilities. CVSS attempts to establish a measurement of how much concern a vulnerability warrants. The CVSS model uses three distinct measurements or scores that include Base, Temporal, and Environmental calculations, each consisting of a set of metrics. The full standard, which is maintained by the Forum of Incident Response and Security Teams (FIRST), can be found at: https://www.first.org/cvss .
NVIDIA follows CVSS v3.1 Specification Document Qualitative Severity Rating Scale (https://www.first.org/cvss/specification-document) to define Severity Ratings as shown in the table below:
| Security Impact Rating | CVSS Score |
| Critical | 9.0 – 10.0 |
| High | 7.0 – 8.9 |
| Medium | 4.0 – 6.9 |
| Low | 0.1 – 3.9 |
| None | 0.0 |
NVIDIA reserves the right to deviate from these guidelines in specific cases if additional factors are not properly captured in the CVSS score.
When and where applicable, NVIDIA Security Bulletins will provide the CVSS v3.1 Base Score. NVIDIA focuses on the Base metric group only, because it will bring the most value to our customers, and represents the intrinsic characteristics of a vulnerability. NVIDIA’s risk assessment is based on an average of risk across a diverse set of installed systems and may not represent the true risk of your local installation.
NVIDIA recommends consulting a security or IT professional to evaluate the risk of your specific configuration and encourages you to compute the Environmental score based on your network parameters. NVIDIA recommends that all customers take into account the Base Score and any Temporal and/or Environmental Scores that may be relevant to their environment to assess their overall risk. This overall score represents a moment in time and is tailored to your specific environment. You should use a security or IT professional’s assessment of the issue and this final score to prioritize responses in your own environment.
Vulnerability Communication Policy
NVIDIA uses the following guidelines for non-third-party software vulnerabilities to determine the appropriate Communication Plan:
| Security Impact Rating | CVSS Score | Communication Plan |
| Critical | 9.0–10.0 | NVIDIA Security Bulletin |
| High | 7.0–8.9 | |
| Medium | 4.0–6.9 | |
| Low | 3.9 or below |
If there is a security issue with a third-party software component that is used in an NVIDIA product, NVIDIA may publish a Security Bulletin. If a Security Bulletin is published for a third-party software component vulnerability, then NVIDIA typically uses the CVSS score provided by the component creator. In some cases, NVIDIA may adjust the CVSS score to reflect the impact to the NVIDIA product.
NVIDIA reserves the right to deviate from these guidelines in specific cases if additional factors are not properly captured in the CVSS score.
Security Bulletins
In most cases, NVIDIA intends to notify customers when there is an identified practical workaround or security update for a security vulnerability. The notification is through either targeted communications or by posting a Security Bulletin. Before posting the Security Bulletin, NVIDIA PSIRT will first complete the vulnerability response process and determine that sufficient software updates or workarounds exist to address the vulnerability, or subsequent public disclosure of remediation is planned to address the vulnerabilities.
Security Bulletins attempt to balance the right amount of information by providing sufficient details so that customers can protect themselves, but not verbose details allowing malicious users to take advantage of the information. NVIDIA Security Bulletins will typically include the following information where applicable:
- Products and versions affected
- Common Vulnerability Enumeration (CVE) identifier for the vulnerability (see https://cve.mitre.org)
- Brief description of the vulnerability and potential impact if exploited
- The Common Vulnerability Scoring System (CVSS) severity rating for the vulnerability (see https://www.first.org/cvss/user-guide.html)
- Remediation details such as security update, mitigation, or other action required by the customer
- Credit to the reporter of the identified vulnerability and acknowledgment for working with NVIDIA on the Coordinated Vulnerability Disclosure
NVIDIA will not provide additional information about the specifics of vulnerabilities beyond what is provided in the Security Bulletin and related documentation such as release notes, knowledge base articles, FAQs, etc. NVIDIA does not distribute exploit/proof of concept code for identified vulnerabilities.
In accordance with industry practices, NVIDIA does not share the findings from internal security testing or other types of security activities with external entities. It is important to note that any scan of NVIDIA’s Security production systems will be considered an attack. If you are an OEM partner, please coordinate your needs with your NVIDIA program manager.
NVIDIA Security Bulletins are posted on the Security Bulletin page. You can subscribe to notifications here.
Security Notice
NVIDIA may release a special communication to respond quickly and appropriately to public disclosures where the vulnerability may have received significant public attention, is likely to have exploits available, or is expected to be actively exploited. In such an event, NVIDIA may expedite the communication and may or may not include a complete set of patches or workarounds. This will be labeled as a Security Notice and posted on the Security Bulletin page.
Vulnerability Remediation
NVIDIA takes security concerns seriously and works to evaluate and address them in a timely manner. Response timelines will depend on many factors, including: the severity, the product affected, the current development cycle, QA cycles, and whether the issue can only be updated in a major release.
Remediation may take one or more of the following forms:
- A new release
- An NVIDIA-provided security update
- Instructions to download and install an update or patch from a third-party
- A workaround to mitigate the vulnerability
Notwithstanding the foregoing, NVIDIA does not guarantee a specific resolution for issues and not all issues identified may be addressed.
NVIDIA PSIRT Participation
Customer Rights: Warranties, Support, and Maintenance
NVIDIA customers’ rights with respect to warranties and support and maintenance, including vulnerabilities, in any NVIDIA software product are governed by the applicable agreement between NVIDIA and each customer.
The statements on this web page do not modify or expand any customer rights or create any additional warranties. Any information provided to NVIDIA regarding vulnerabilities in NVIDIA products including all information in a product vulnerability report shall become the sole information of NVIDIA.
Disclaimer
All aspects of NVIDIA’s PSIRT process and policies are subject to change without notice and on a case-by-case basis. Response is not guaranteed for any specific issue or class of issues. Your use of the information on the document or materials linked from the document is at your own risk. NVIDIA reserves the right to change or update this document without notice at any time.
ALL NVIDIA INFORMATION, DESIGN SPECIFICATIONS, REFERENCE BOARDS, FILES, DRAWINGS, DIAGNOSTICS, LISTS, AND OTHER DOCUMENTS (TOGETHER AND SEPARATELY, “MATERIALS”) ARE BEING PROVIDED “AS IS.” NVIDIA MAKES NO WARRANTIES, EXPRESS, IMPLIED, STATUTORY, OR OTHERWISE WITH RESPECT TO THE MATERIALS, AND ALL EXPRESS OR IMPLIED CONDITIONS, REPRESENTATIONS AND WARRANTIES, INCLUDING ANY IMPLIED WARRANTY OR CONDITION OF TITLE, MERCHANTABILITY, SATISFACTORY QUALITY, FITNESS FOR A PARTICULAR PURPOSE AND NON-INFRINGEMENT, ARE HEREBY EXCLUDED TO THE MAXIMUM EXTENT PERMITTED BY LAW.
Information is believed to be accurate and reliable at the time it is furnished. However, NVIDIA Corporation assumes no responsibility for the consequences of use of such information or for any infringement of patents or other rights of third parties that may result from its use. No license is granted by implication or otherwise under any patent or patent rights of NVIDIA Corporation. Specifications mentioned in this publication are subject to change without notice. This publication supersedes and replaces all information previously supplied. NVIDIA Corporation products are not authorized for use as critical components in life support devices or systems without express written approval of NVIDIA Corporation.